Enable single sign-on
Enable single sign-on¶
Users are shared between MKE and MSR by default, but the applications have separate browser-based interfaces which require authentication.
To only authenticate once, you can configure MSR to have single sign-on (SSO) with MKE.
Note
After configuring single sign-on with MSR, users accessing
MSR via docker login should create an access
token and use it to authenticate.
At install time¶
When installing MSR, pass
--dtr-external-url <url> to enable SSO. Specify the Fully Qualified
Domain Name (FQDN) of your MSR, or
a load balancer, to load-balance requests across multiple MSR replicas.
docker run --rm -it \
docker/dtr:2.7.5 install \
--dtr-external-url dtr.example.com \
--dtr-cert "$(cat cert.pem)" \
--dtr-ca "$(cat dtr_ca.pem)" \
--dtr-key "$(cat key.pem)" \
--ucp-url ucp.example.com \
--ucp-username admin \
--ucp-ca "$(cat ucp_ca.pem)"
This makes it so that when you access MSR’s web user interface, you are redirected to the MKE login page for authentication. Upon successfully logging in, you are then redirected to your specified MSR external URL during installation.
Post-installation¶
Web user interface¶
Navigate to
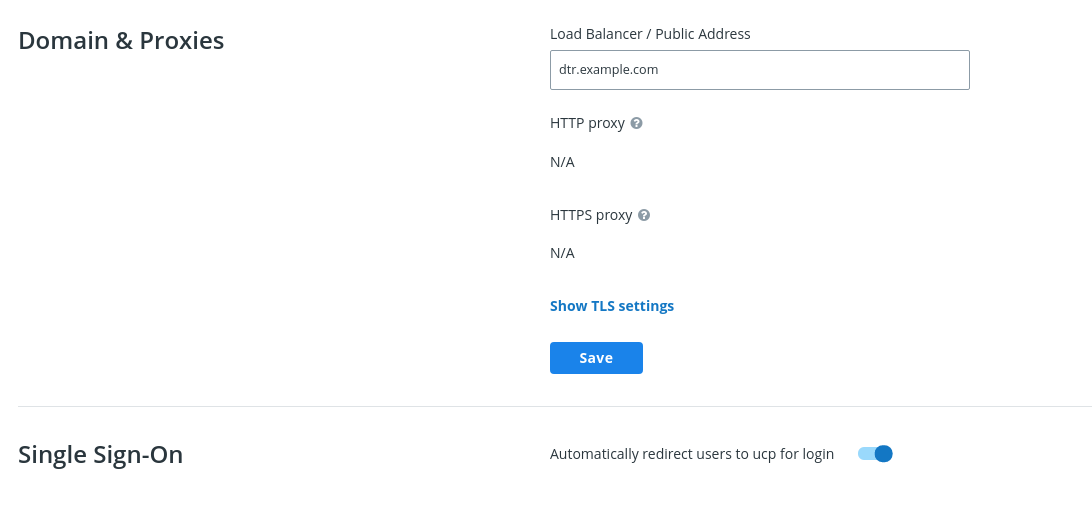
https://<msr-url>and log in with your credentials.Select System from the left navigation pane, and scroll down to Domain & Proxies.
Update the Load balancer / Public Address field with the external URL where users should be redirected once they are logged in. Click Save to apply your changes.
Toggle Single Sign-on to automatically redirect users to MKE for logging in.
Command line interface¶
You can also enable single sign-on from the command line by reconfiguring your MSR. To do so, run the following:
docker run --rm -it \
docker/dtr:2.7.5 reconfigure \
--dtr-external-url dtr.example.com \
--dtr-cert "$(cat cert.pem)" \
--dtr-ca "$(cat dtr_ca.pem)" \
--dtr-key "$(cat key.pem)" \
--ucp-url ucp.example.com \
--ucp-username admin \
--ucp-ca "$(cat ucp_ca.pem)"