Manage applications¶
With the introduction of the experimental app plugin to the Docker CLI, MSR has been enhanced to include application management. Starting from MSR 2.7, you can push an app to your MSR repository and have an application be clearly distinguished from individual and multi-architecture container images as well as plugins. When you push an application to MSR, you see two image tags:
Image |
Tag |
Type |
Under the hood |
|---|---|---|---|
Invocation |
|
Container image represented by OS and architecture (e.g.
|
Uses Mirantis Container Runtime. The Docker daemon is responsible for building and pushing the image. |
Application with bundled components |
|
Application |
Uses the app client to build and push the image. |
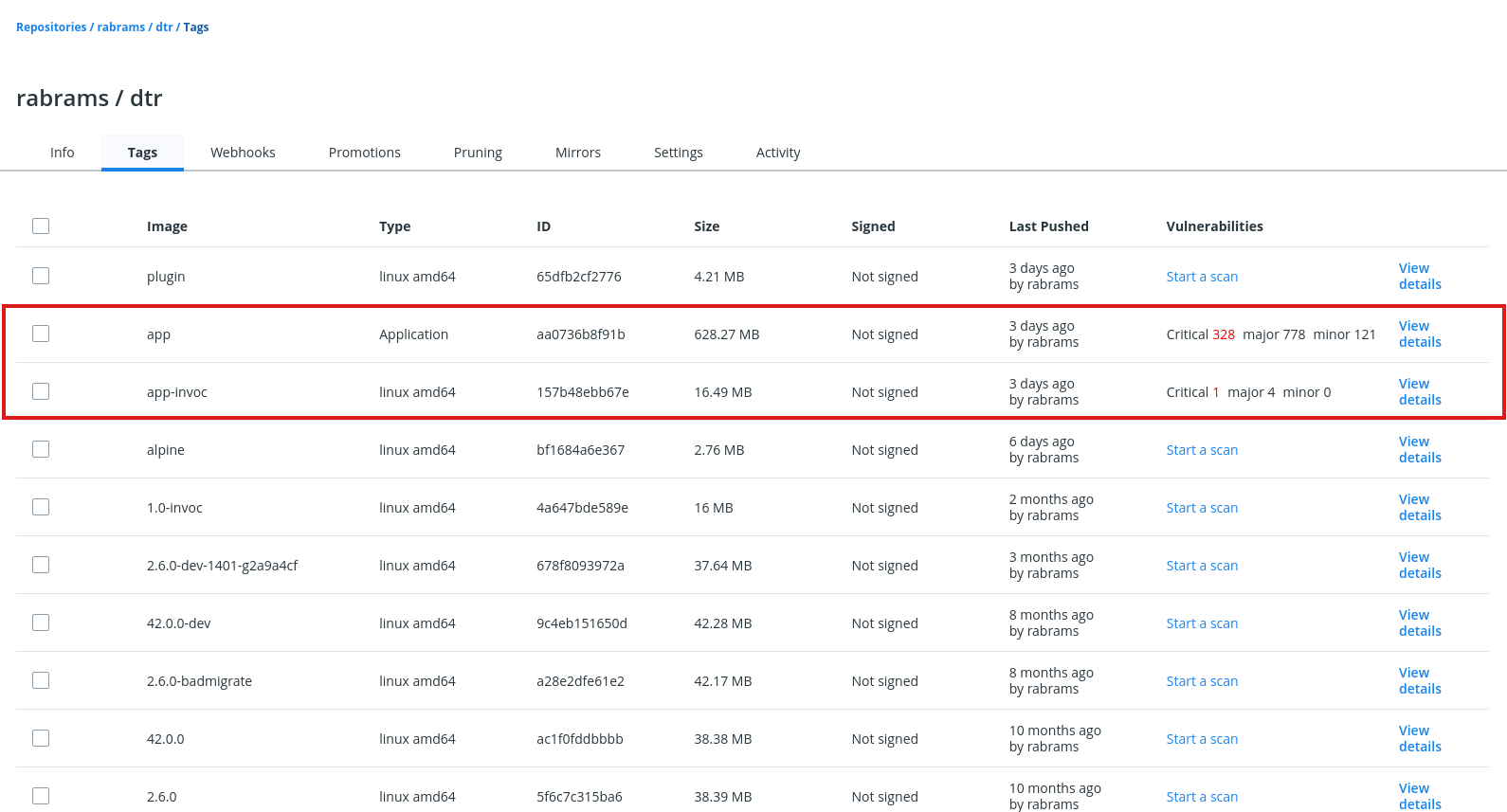
Notice the app-specific tags, app and app-invoc, with scan
results for the bundled components in the former and the invocation
image in the latter. To view the scanning results for the bundled
components, click “View Details” next to the app tag.
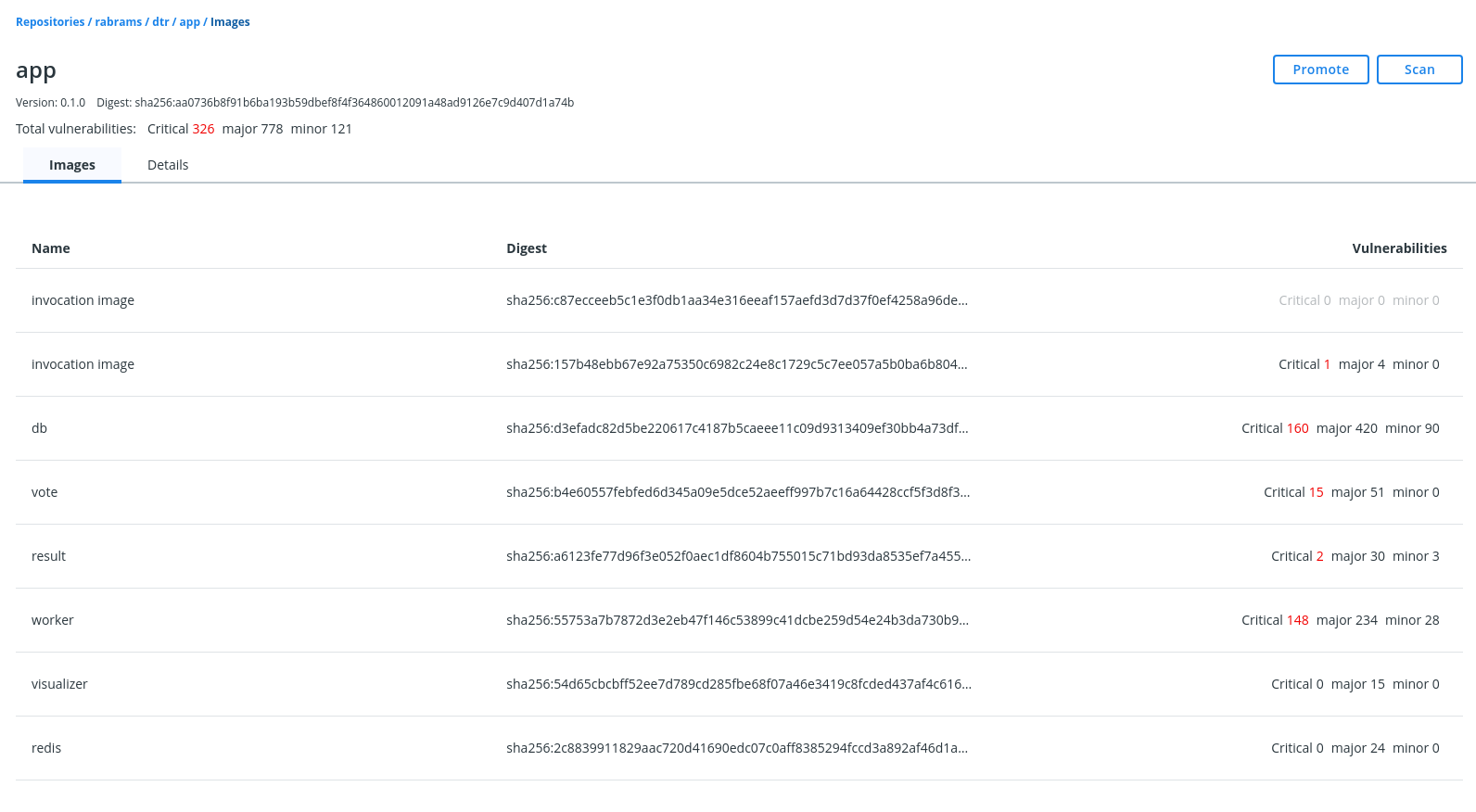
Click on the image name or digest to see the vulnerabilities for that specific image.
Parity with existing repository and image features¶
The following repository and image management events also apply to applications:
Creation
MSR pushes
Limitations¶
You cannot sign an application since the Notary signer cannot sign OCI (Open Container Initiative) indices.
Scanning-based policies do not take effect until after all images bundled in the application have been scanned.
Docker Content Trust (DCT) does not work for applications and multi-arch images, which are the same under the hood.
Troubleshooting tips¶
x509 certificate errors¶
fixing up "35.165.223.150/admin/lab-words:0.1.0" for push: failed to resolve "35.165.223.150/admin/lab-words:0.1.0-invoc", push the image to the registry before pushing the bundle: failed to do request: Head https://35.165.223.150/v2/admin/lab-words/manifests/0.1.0-invoc: x509: certificate signed by unknown authority
Workaround¶
Check that your MSR has been configured with your TLS certificate’s Fully Qualified Domain Name (FQDN).
For docker app testing purposes, you can pass the
--insecure-registries option for pushing an application`.
docker app push hello-world --tag 35.165.223.150/admin/lab-words:0.1.0 --insecure-registries 35.165.223.150
35.165.223.150/admin/lab-words:0.1.0-invoc
Successfully pushed bundle to 35.165.223.150/admin/lab-words:0.1.0. Digest is sha256:bd1a813b6301939fa46e617f96711e0cca1e4065d2d724eb86abde6ef7b18e23.
Known Issues¶
See MSR 2.7 Release Notes for known issues related to applications in MSR.